Exercises, examples and other material relating to training module A162. This topic is presented on public courses
You should take regular backups of most computer systems so that you don't lose your work in the event of a security breach, hardware failure of user error. This module examines the how, when and why of backups (and how to restore) and other day-to-day file system maintenance issues.
| Articles and tips on this subject | updated |
| 4481 | Extracting data from backups to restore selected rows from MySQL tables
We take backups from our live server, using mysqldump for the databases, and tar / gzip for most of the file systems. And when we had a server failure which meant a reload (and a new underlying OS too), we were able to be back online in a couple of hours, with minimal data loss.
But our backups are ... | 2015-05-02
|
| 4405 | Backup procedures - via backup server
Our main web server system becomes ever more important to our business - and having procedures in place to restore systems in the event of failure becomes ever more critical.
What are we protecting against? Both hardware and software failures, and against intrusions and obsolescence (to the extent of ... | 2015-01-24
|
| 4400 | Commenting out an echo killed my bash backup script
"Commenting out an echo killed my bash script" - yes, really!
Here (with password amended!) is part of my bash script which takes a database snapshot from time to time - and it's been running well over a 24 hour cycle, giving me checkpoints to return to. But it was getting a bit verbose, so I added ... | 2015-01-19
|
| 4390 | Checking MySQL database backups have worked (not failed)
We do a regular backup of of MySQL databases within our server to keep recent local data "checkpoint" sets there - they allow us to look back at what the data used to be if we have a naughty user, and in the worst case scenario of a software problem / database corruption we can roll back. However we've ... | 2015-01-12
|
| 4115 | More or less back - what happened to our server the other day
I woke Wednesday morning to an email informing me that one of our two dedicated root servers had been identified as being involved in a Distributed Denial of Service attack and that the hosting centre where it's based (and the company from whom we lease it) would be taking the system offline (said "had", ... | 2013-06-15
|
| 4063 | Backups by crossover between network centres - setting up automatic scp transfers
Our web servers don't need transaction logging backup systems - emails and secure pages are looked after (and spam trapped) by a separate machine from our two dedicated web servers, which handle a great deal of requests for data reads, but data writes aren't all that many. But of course the data writes ... | 2013-04-20
|
| 4056 | An overpractical test of our backup strategy!
Exercises are all very well - but the real test of how your emergency procedures work are in a real emergency. So it was that at 3 O'Clock this morning I noted something very odd with our server load; logged in and noticed a process called "shred" running a root and got chucked off about 60 seconds later. ... | 2013-04-06
|
| 593 | Finding where the disc space has gone
Murphy's fourth law states that data expands to fill the disc space available, and there's a collaboration that states that it reaches that full point when you're trying to save a file you should have saved a long time ago during a complex operation.
I'm not a good one at deleting old backup files; ... | 2012-11-04
|
| 2299 | How much space does my directory take - Linux
The index card in the library for "War and Peace" takes a lot less space that the book itself, and so it is when you ask Linux or Unix "how much space is taken in this directory" ... you'll be told how big each of the files are, and how big the index table for each subrirectory is. Here's an example ... | 2009-07-22
|
| 1288 | Linux run states, shell special commands, and directory structures
Some useful notes from the board ...
Run states of Unix and Linux systems:
0 - Halted
1 - Single User
2 - Multiuser
3 - Full Multiuser (inc servers)
5 - Same + X Windows
6 - transient reboot
Install Order for LAMP
Linux ...
... then Apache httpd
... then MySQL
... then PHP.
PHP must be after MySQL ... | 2009-01-22
|
| 1893 | Some Linux and Unix tips
How to make a woman equal to a man
[trainee@easterton ~]$ man ls
[trainee@easterton ~]$ woman ls
-bash: woman: command not found
[trainee@easterton ~]$ alias woman=man
[trainee@easterton ~]$ woman ls
[trainee@easterton ~]$
In Linux and Unix, the man command gives you a manual page ... but there is ... | 2008-11-18
|
| 1801 | Will your backups work if you have to restore them?
There are a lot of myths surrounding data backups. Ones says that "the more often you take backup everything, the better it is", but actually that only applies to data that's changing. There is little point in wasting a lot of resources repeatedly backing up the same unchanging builds in /usr/local ... | 2008-09-22
|
| 1765 | Dialects of English and Unix
English is spoken as a first language by over 300 million people, and by about five times that number if you include people who can speak it as a second or third language. But that doesn't mean that word and wording is going to be the same within different variants, let alone the subtleties and drifts, ... | 2008-08-22
|
| 1648 | The tourists guide to Linux
When visitors come to this country for a touring holiday, they'll land at Gatwick and take in London, Stonehenge, Bath, Stratord-upon-Avon, York (pehaps) and Edinburgh. That will give them a flavour but none of the details (and of course they'll miss gems such as Melksham and Radstock). But they will ... | 2008-05-20
|
| 1439 | Linux / Unix - layout of operating system files
At the top level ..
Typically "read only"
bin - binaries - executable programs
sbin - system admin binaries - programs for the system / admin
lib - library files (needed by binaries and shared between them)
usr - the bulk of the operating system (the bit that is not needed to boot)
Typically "read ... | 2007-11-20
|
| 1023 | Finding public writeable things on your linux file system
Wondering what files and directories on your (Unix, Linux, OS X) system are marked "public writeable"?
There should be very few indeed (none is good), but the following will wheedle them out.
find . -perm -2 -print
""Find, under the current directory ('.') all symbols with permission bit "2" set, ... | 2007-01-06
(short) |
| 1013 | Copy multiple files - confusing error message from cp
Thought you might like me to share this one ...
Copying a whole series of files into a directory (Linux, Unix, OS X) using cp, you give a whole series of source files followed by the name of the target directory. Add the -r option is you want to specify subdirectories to be copied recursively in your ... | 2006-12-30
|
| 754 | tar, jar, war, ear, sar files
Have you ever wondered why that are so many file extensions ending in "a r"? It's because the "ar" stands for archive, and it's such a reasonable way of naming file that the original tar which stands for tape archive was picked up by Sun and the Java community and transmuted into other file formats.
tar ... | 2006-06-13
|
| 554 | What backup is adequate?
I've been ski-ing for the last 5 days. Or rather - trying too. On one day, the slopes were completely closed and on the other days there has only been limited opening - of the 30 lifts perhaps 10 have been running on average, and this is peak season. Yesterday, we went to the Gondola Station here in ... | 2006-06-09
|
| 153 | Linux - where to put swap space
Swap Space is used on Unix and Linux systems to provide additional pseudomemory resources. In other words, if you try to run so many processes that they won't all fit into memory at the same time, the operating system will swap them in and out of the swap space.
Swap space can be either disc partition(s) ... | 2006-06-05
|
| 703 | Copying files and preserving ownership
If you're copying a file on a Unix / Linux / OS X operating system, use the cp command. Use cp -r to copy a directory and all its contents - the -r means "recursive". If you use the cp command to copy files that you have read access to, but do not own, then you'll be made the owner of the new copies; ... | 2006-06-05
|
| 735 | Boys will be boys, saved by Ubuntu
Many things were very different in the 1960s to the way they are today. Rosey-tinted spectacles, looking back on what's perceived as a golden age, may persuade many that life simpler and better back then, and there's a saying that "School days are the happiest days of your life". Well - I've news for ... | 2006-05-30
|
Some modules are
available for download as a sample of our material or under an
Open Training Notes License for free download from
[here].
Backup schemes and the need to backup.
Dump and restore.
Tar.
CPIO, dd and other tools.
Backup strategies.
Mounting file systems and monitoring usage.
Symbolic links.
Hard links.
Finding files.
Some more useful commands.
If you are looking for a complete course and not just a information on a single subject, visit our
Listing and schedule page.
Well House Consultants specialise in training courses in
Linux and LAMP,
Ruby,
Lua,
Python,
Perl,
PHP, and
MySQL. We run
Private Courses throughout the UK (and beyond for longer courses), and
Public Courses at our training centre in Melksham, Wiltshire, England.
It's surprisingly cost effective to come on our public courses -
even if
you live in a different
country or continent to us.
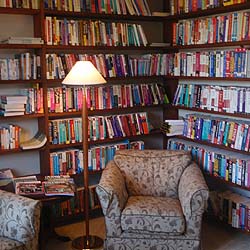
We have a technical library of over 700 books on the subjects on which we teach.
These books are available for reference at our training centre.